Data Processing Addendum
Last updated: May 10, 2026
This Data Processing Addendum (“DPA”) forms part of the Syrix Terms of Service, order form, subscription agreement, partner agreement, or other written agreement governing Customer’s use of the Syrix Services (the “Agreement”).
This DPA applies when Syrix, doing business as Syrix (“Syrix,” “we,” “our,” or “us”), processes Personal Data on behalf of Customer in connection with the Services.
If there is a conflict between this DPA and the Agreement regarding the processing of Personal Data, this DPA controls to the extent of the conflict.
Table of Contents
- Definitions
- Roles of the parties
- Scope of processing
- Customer instructions
- Customer responsibilities
- Syrix processing obligations
- Confidentiality
- Security measures
- Subprocessors
- International data transfers
- Assistance with data subject requests
- Assistance with compliance obligations
- Personal Data Breach notification
- Deletion and return of Personal Data
- Audits and information rights
- Government and third-party requests
- MSP and partner use
- Use of aggregated or de-identified data
- Order of precedence
- Contact Schedule 1 — Details of Processing Schedule 2 — Subprocessors Schedule 3 — Technical and Organizational Measures Schedule 4 — International Transfers
1. Definitions
For purposes of this DPA:
“Applicable Data Protection Laws” means all privacy, data protection, and data security laws and regulations applicable to the processing of Personal Data under the Agreement, which may include the GDPR, UK GDPR, applicable U.S. state privacy laws, applicable Israeli privacy law, and other applicable privacy laws.
“Customer” means the organization or person that has entered into the Agreement with Syrix and uses the Services.
“Customer Data” has the meaning given in the Agreement and includes data, content, metadata, logs, configuration information, account information, tenant information, security information, and other materials submitted to, connected to, generated by, or processed through the Services on behalf of Customer.
“Customer Environment” means a Microsoft 365 tenant, Microsoft Entra ID tenant, cloud environment, SaaS environment, or other protected environment connected to or monitored by Syrix on behalf of Customer.
“Data Subject,” “Controller,” “Processor,” “Subprocessor,” “Personal Data,” “Personal Data Breach,” “Process,” “Processing,” and “Supervisory Authority” have the meanings given under Applicable Data Protection Laws. Where Applicable Data Protection Laws use equivalent terms, such as “business,” “service provider,” “contractor,” “consumer,” or “personal information,” those terms will be interpreted consistently with the applicable law.
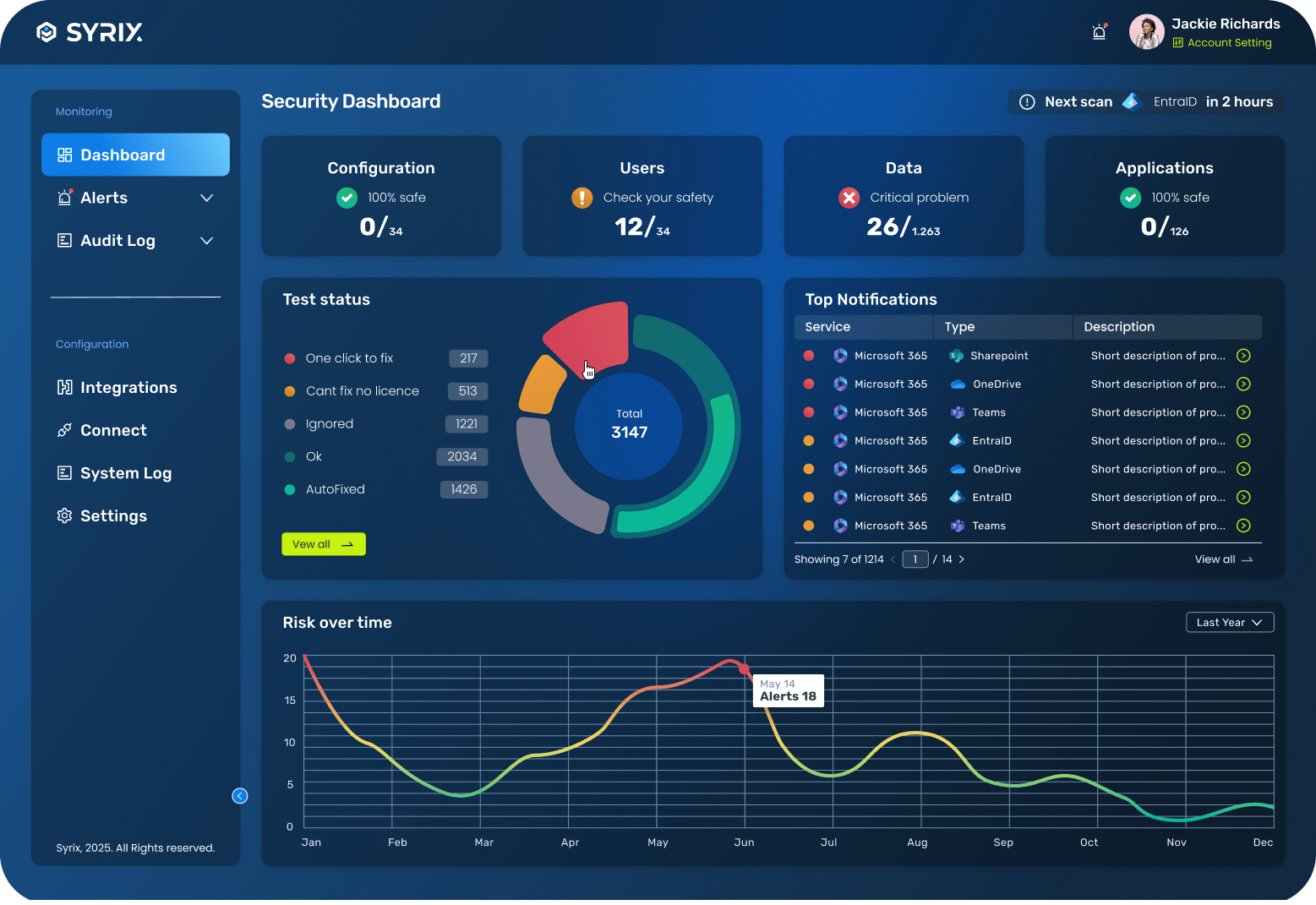
“Services” means the Syrix websites, web application, platform, products, services, trials, subscriptions, documentation, and related offerings provided under the Agreement.
“Standard Contractual Clauses” or “SCCs” means the standard contractual clauses approved by the European Commission for international transfers of Personal Data, as updated, replaced, or supplemented from time to time.
“UK Addendum” means the International Data Transfer Addendum issued by the UK Information Commissioner’s Office, as updated, replaced, or supplemented from time to time.
2. Roles of the parties
2.1 Customer as Controller
For Personal Data processed by Syrix on behalf of Customer through the Services, Customer is the Controller and Syrix is the Processor, unless otherwise required by Applicable Data Protection Laws.
Customer determines the purposes and means of Processing Personal Data in Customer Data, including Personal Data from Customer Environments.
2.2 Syrix as Processor
Syrix Processes Personal Data on behalf of Customer to provide, operate, secure, support, and improve the Services according to Customer’s instructions and the Agreement.
2.3 Syrix as Controller
Syrix may act as an independent Controller for certain Personal Data processed outside the processor relationship, such as website visitor data, sales and marketing contacts, billing contacts, account administration data, security and operational data needed to protect Syrix, and business relationship records. Such processing is described in the Syrix Privacy Policy and is not governed by this DPA except where expressly stated.
3. Scope of processing
The subject matter, duration, nature, purpose, categories of Personal Data, and categories of Data Subjects are described in Schedule 1 — Details of Processing.
Customer authorizes Syrix to Process Personal Data as necessary to provide the Services, including to:
- Connect to Customer Environments authorized by Customer.
- Evaluate security posture, configurations, access, permissions, apps, sharing, audit logs, alerts, and related security metadata.
- Generate findings, recommendations, remediation previews, security logs, audit logs, access review evidence, compliance evidence, reports, and exports.
- Perform remediation actions authorized by Customer or configured by Customer for automatic execution.
- Provide product functionality, support, troubleshooting, security, monitoring, availability, backup, recovery, and service improvement.
- Comply with applicable legal, security, and contractual obligations.
4. Customer instructions
Customer instructs Syrix to Process Personal Data as necessary to provide the Services under the Agreement and this DPA.
Customer’s instructions include:
- The Agreement.
- This DPA.
- Customer’s use and configuration of the Services.
- Permissions and integrations authorized by Customer.
- Remediation, approval, suppression, rollback, retention, export, and other workflow decisions made by Customer or its authorized users.
- Written instructions mutually agreed by the parties.
Syrix will not Process Personal Data for purposes other than those described in the Agreement, this DPA, or Customer’s documented instructions, unless required by law. If Syrix is required by law to Process Personal Data contrary to Customer’s instructions, Syrix will notify Customer unless legally prohibited from doing so.
If Syrix believes that an instruction violates Applicable Data Protection Laws, Syrix will inform Customer where legally permitted. Syrix may suspend Processing affected by such instruction until the issue is resolved.
5. Customer responsibilities
Customer is responsible for:
- Complying with Applicable Data Protection Laws.
- Having a lawful basis for collecting, using, sharing, and Processing Personal Data through the Services.
- Providing notices and obtaining consents where required.
- Ensuring that Customer has the right to authorize Syrix to access and Process Personal Data from Customer Environments.
- Ensuring that Customer’s instructions to Syrix are lawful.
- Configuring access permissions, integrations, retention, remediation, and user roles appropriately.
- Managing authorized users and preventing unauthorized access.
- Responding to Data Subject requests where Customer is the Controller.
- Ensuring that Personal Data submitted to the Services is appropriate and not excessive for the Services.
Customer will not submit special categories of Personal Data, highly sensitive Personal Data, or regulated data to the Services unless necessary for Customer’s use of the Services and permitted under the Agreement, this DPA, and Applicable Data Protection Laws.
6. Syrix processing obligations
Syrix will:
- Process Personal Data only according to Customer’s documented instructions.
- Ensure that personnel authorized to Process Personal Data are subject to appropriate confidentiality obligations.
- Implement appropriate technical and organizational measures designed to protect Personal Data.
- Assist Customer with Data Subject requests, security obligations, breach notification obligations, data protection impact assessments, and consultations with Supervisory Authorities, as required by Applicable Data Protection Laws and taking into account the nature of the Processing and information available to Syrix.
- Use Subprocessors only as described in this DPA.
- Delete or return Personal Data as described in this DPA and the Agreement.
- Make available information reasonably necessary to demonstrate compliance with this DPA, subject to the audit terms below.
7. Confidentiality
Syrix will ensure that persons authorized to Process Personal Data are bound by confidentiality obligations or are under an appropriate statutory obligation of confidentiality.
Syrix will restrict access to Personal Data to personnel, contractors, advisors, service providers, and Subprocessors who need access to provide, secure, support, or operate the Services.
8. Security measures
Syrix will implement and maintain appropriate technical and organizational measures designed to protect Personal Data against accidental or unlawful destruction, loss, alteration, unauthorized disclosure, or access.
The measures are described in Schedule 3 — Technical and Organizational Measures.
Customer acknowledges that security measures may evolve over time. Syrix may update or modify its security measures, provided that such updates do not materially decrease the overall security of the Services during an active subscription term.
9. Subprocessors
Customer authorizes Syrix to use Subprocessors to provide, secure, support, and improve the Services.
Syrix will enter into a written agreement with each Subprocessor that imposes data protection obligations no less protective, in substance, than those in this DPA, to the extent applicable to the services provided by the Subprocessor.
A current list of Syrix Subprocessors is set out in Schedule 2 — Subprocessors. Customer may request the current list or additional subprocessor information by contacting dpa@syrix.io.
Syrix may update its Subprocessor list from time to time. Where required by Applicable Data Protection Laws or the Agreement, Syrix will provide notice of new Subprocessors before authorizing them to Process Personal Data.
Customer may object to a new Subprocessor on reasonable data protection grounds by notifying Syrix within 15 days after notice. The parties will work in good faith to resolve the objection. If the objection cannot be resolved, Customer may terminate the affected Services to the extent the new Subprocessor is necessary for those Services. Unless otherwise required by law or agreed in writing, termination under this section will not entitle Customer to a refund for Services already provided.
Syrix remains responsible for the performance of its Subprocessors’ obligations as required by Applicable Data Protection Laws.
10. International data transfers
Syrix and its Subprocessors may Process Personal Data in multiple jurisdictions where Syrix or its Subprocessors operate.
Where Personal Data is transferred internationally, Syrix will use appropriate transfer mechanisms as required by Applicable Data Protection Laws. These mechanisms may include adequacy decisions, data processing agreements, the SCCs, the UK Addendum, contractual safeguards, or other lawful transfer mechanisms.
Additional international transfer terms are described in Schedule 4 — International Transfers.
11. Assistance with data subject requests
Taking into account the nature of the Processing and the information available to Syrix, Syrix will provide reasonable assistance to Customer in responding to requests from Data Subjects to exercise rights under Applicable Data Protection Laws.
If Syrix receives a request directly from a Data Subject relating to Personal Data processed on behalf of Customer, Syrix may refer the request to Customer unless otherwise required by law. Syrix will not independently respond to such requests except to confirm that the request relates to Customer or as legally required.
Customer is responsible for responding to Data Subject requests where Customer is the Controller.
12. Assistance with compliance obligations
Taking into account the nature of the Processing and information available to Syrix, Syrix will provide reasonable assistance to Customer with Customer’s obligations under Applicable Data Protection Laws, including obligations relating to:
- Security of Processing.
- Personal Data Breach notifications.
- Data protection impact assessments.
- Prior consultation with Supervisory Authorities, where required.
Syrix may charge reasonable fees for assistance that is outside the standard functionality of the Services or requires substantial additional effort, unless the assistance is required due to Syrix’s breach of this DPA.
13. Personal Data Breach notification
Syrix will notify Customer without undue delay after becoming aware of a Personal Data Breach affecting Personal Data processed by Syrix on behalf of Customer, and in any event within 72 hours after becoming aware of the Personal Data Breach, unless legally prohibited or where notification is not reasonably possible within that timeframe due to the nature of the incident.
The notification will include information reasonably available to Syrix, which may include:
- The nature of the Personal Data Breach.
- The categories and approximate number of affected Data Subjects, where known.
- The categories and approximate number of affected records, where known.
- Likely consequences, where known.
- Measures taken or proposed to address the Personal Data Breach.
- Contact information for follow-up.
Syrix’s notification of or response to a Personal Data Breach is not an admission of fault or liability.
Customer is responsible for determining whether notification to Data Subjects, Supervisory Authorities, customers, regulators, or other third parties is required.
14. Deletion and return of Personal Data
Upon termination or expiration of the Services, Syrix will delete or return Personal Data processed on behalf of Customer according to the Agreement, product functionality, Customer configuration, and applicable law.
Unless otherwise agreed in writing or required by law, Syrix will delete or anonymize Customer tenant data within a reasonable period after termination or expiration of the Services.
Syrix may retain Personal Data where required or permitted for legal, security, compliance, dispute-resolution, backup, audit, accounting, or legitimate business purposes, subject to the confidentiality and security obligations in this DPA.
Backups may retain Personal Data for a limited period according to Syrix’s backup and disaster recovery practices before being overwritten or deleted.
15. Audits and information rights
Syrix will make available information reasonably necessary to demonstrate compliance with this DPA.
Where available, Syrix may satisfy audit requests by providing security documentation, compliance reports, certifications, third-party audit summaries, questionnaires, or other relevant materials.
Customer may request an audit no more than once per calendar year, unless required by a Supervisory Authority or following a confirmed Personal Data Breach affecting Customer Personal Data.
Any audit must be:
- Conducted on reasonable prior written notice.
- Limited to Syrix’s Processing of Personal Data on behalf of Customer.
- Conducted during normal business hours.
- Subject to confidentiality obligations.
- Designed to avoid unreasonable disruption to Syrix’s business, systems, security, and other customers.
Customer may not access data, systems, or information relating to other Syrix customers. Syrix may require audits to be conducted by an independent third-party auditor that is not a competitor of Syrix.
Customer will bear its own audit costs. Syrix may charge reasonable fees for support with audits that require substantial additional effort, unless the audit is required due to Syrix’s breach of this DPA.
16. Government and third-party requests
If Syrix receives a legally binding request from a government authority, court, regulator, law enforcement agency, or third party seeking access to Personal Data processed on behalf of Customer, Syrix will notify Customer unless legally prohibited from doing so.
Syrix will make reasonable efforts to redirect the requesting party to Customer where appropriate and legally permitted.
17. MSP and partner use
If Customer uses the Services on behalf of Managed Clients, Customer is responsible for ensuring that it has all rights, permissions, notices, consents, agreements, and instructions needed to authorize Syrix to Process Personal Data from Managed Client environments.
As between Syrix and Customer, Customer is responsible for its Managed Clients and for ensuring that Customer’s use of the Services complies with all applicable data protection obligations owed to those Managed Clients.
Customer will not represent that Syrix has a direct processor relationship with a Managed Client unless Syrix has separately agreed in writing.
18. Use of aggregated or de-identified data
Syrix may create and use aggregated or de-identified data derived from the Services, provided that such data does not identify Customer, Customer’s users, Managed Clients, or any individual.
Syrix may use aggregated or de-identified data for analytics, benchmarking, product improvement, security research, threat analysis, and business purposes.
19. Order of precedence
If there is a conflict between documents regarding the Processing of Personal Data, the following order applies:
- Standard Contractual Clauses or other mandatory transfer terms, where applicable.
- This DPA.
- The Agreement.
- The Privacy Policy.
- Product documentation or website materials.
20. Contact
For data processing inquiries, contact:
Email: dpa@syrix.io
For privacy requests, contact:
Email: privacy@syrix.io
For security matters, contact:
Email: security@syrix.io
Legal entity: [Insert Syrix legal entity name]
Schedule 1 — Details of Processing
1. Subject matter
Syrix’s Processing of Personal Data on behalf of Customer in connection with the provision of the Syrix cloud security platform and related Services.
2. Duration
For the duration of Customer’s subscription, trial, pilot, beta, or other use of the Services, plus any post-termination period required for deletion, return, backup retention, legal compliance, dispute resolution, audit, or security purposes.
3. Nature of Processing
Syrix may perform the following Processing activities:
- Collection and retrieval.
- Connection to Customer Environments.
- Reading and evaluation of configuration, identity, access, app, security, audit, sharing, and compliance metadata.
- Hosting and storage.
- Analysis and correlation.
- Monitoring and alerting.
- Report and evidence generation.
- Logging and audit trail creation.
- Remediation preview and execution.
- Approval, suppression, rollback, and recovery workflow processing.
- Export and display within the Services.
- Support, troubleshooting, maintenance, backup, security, and service improvement.
- Deletion, anonymization, or return.
4. Purpose of Processing
The purpose of Processing is to provide the Services, including:
- Security posture management.
- Microsoft 365 configuration monitoring.
- Misconfiguration detection.
- Configuration drift detection.
- Automated and guided remediation.
- Access governance.
- Guest and privileged user access reviews.
- Connected app and OAuth permission visibility.
- Security logging and audit logging.
- Rollback and recovery features.
- Compliance mapping and audit evidence.
- Detection and response workflows, where available.
- Customer support and service operations.
5. Categories of Data Subjects
Personal Data may relate to:
- Customer administrators.
- Customer employees.
- Customer contractors.
- Customer service accounts where associated with identifiable individuals.
- Customer guests and external collaborators.
- Customer users of Microsoft 365 or other connected environments.
- MSP, partner, reseller, or consultant users.
- Managed Client users, where applicable.
- Customer support contacts.
- Customer billing or business contacts.
6. Categories of Personal Data
Personal Data may include:
- Name, display name, username, email address, UPN, user ID, object ID, tenant ID, account ID, role, group membership, and administrator role metadata.
- Business contact details.
- Authentication and access metadata.
- MFA, Conditional Access, password policy, and identity security configuration metadata.
- Guest access, external sharing, link sharing, permission, and access metadata.
- Application, OAuth, service principal, app consent, publisher, permission, and activity metadata.
- Audit logs, security logs, sign-in logs, alert metadata, and event metadata.
- Remediation records, approval decisions, suppressions, rollback records, recovery records, and policy decisions.
- Access review records, attestation records, compliance evidence, and export data.
- Support ticket content and diagnostic data.
- IP address, device, browser, and usage metadata associated with platform use.
7. Sensitive or special category data
The Services are not designed to intentionally collect or process special categories of Personal Data or highly sensitive personal data.
However, such data may appear incidentally in Customer Data, logs, file names, group names, user attributes, support requests, audit records, or metadata provided by Customer or Customer’s connected environments.
Customer is responsible for avoiding unnecessary submission of sensitive data to the Services and for ensuring that any such Processing is lawful.
8. Processing frequency
Continuous, periodic, event-based, and customer-initiated Processing, depending on Customer configuration, product features, scan schedules, integrations, and support needs.
Schedule 2 — Subprocessors
Syrix uses Subprocessors to provide, secure, support, and improve the Services. The list below should be completed and kept current before publication.
Current Subprocessors
Subprocessor | Purpose | Data processed | Location / transfer safeguard |
Amazon Web Services (AWS) | Cloud hosting, infrastructure, storage, networking, security, backups | Customer account data, platform data, Customer Environment metadata, logs, security evidence, operational data | [Insert region / safeguards] |
Microsoft 365 | Internal business productivity, email, document collaboration, customer communications | Business contact data, customer communications, support/security/DPA correspondence, internal documents | [Insert region / safeguards] |
Customer-authorized integrations
Customer-authorized integrations are not listed as Subprocessors solely because Customer connects them to Syrix. They are Customer-designated data sources and protected environments used to provide the Services.
Integration | Role | Data processed |
Microsoft 365 / Microsoft Entra ID | Customer-authorized protected environment and data source | Microsoft 365 configuration, identity, role, guest, sharing, audit, security, app consent, and remediation metadata as authorized by Customer |
Schedule 3 — Technical and Organizational Measures
Syrix will maintain appropriate technical and organizational measures designed to protect Personal Data processed on behalf of Customer.
1. Access control
- Role-based access controls.
- Least-privilege access practices.
- Administrative access restricted to authorized personnel.
- Access reviews for personnel with elevated access, where applicable.
- Removal or adjustment of access when no longer needed.
2. Authentication and authorization
- Authentication controls for Syrix personnel and platform users.
- Support for secure login methods where available.
- Protection of administrative interfaces.
- Controls designed to prevent unauthorized access to customer accounts and environments.
3. Encryption
- Encryption in transit using industry-standard protocols.
- Encryption at rest for production systems where supported by the underlying infrastructure and service architecture.
- Secure handling of credentials, tokens, and secrets.
4. Logging and monitoring
- Logging of relevant administrative, security, and operational events.
- Monitoring for suspicious or unauthorized activity affecting the Services.
- Use of logs for troubleshooting, security, audit, and service integrity.
5. Segregation of customer data
- Logical separation of customer accounts and tenant data.
- Controls designed to prevent unauthorized access between customer environments.
- Multi-tenant access controls for MSP and partner use, where applicable.
6. Secure development and change management
- Secure development practices appropriate to the nature of the Services.
- Review and testing of material changes before production deployment, where appropriate.
- Change tracking and deployment controls.
7. Vulnerability and risk management
- Reasonable measures to identify, assess, and address vulnerabilities.
- Security updates and patching according to risk and operational requirements.
- Review of security-relevant third-party dependencies where appropriate.
8. Backup and recovery
- Backup and recovery practices designed to support availability and resilience.
- Backup retention according to Syrix’s operational practices.
- Recovery procedures tested or reviewed periodically, where appropriate.
9. Personnel security
- Confidentiality obligations for personnel with access to Personal Data.
- Access limited to personnel with a business need.
- Security awareness or training appropriate to roles, where applicable.
10. Subprocessor management
- Review of Subprocessors that Process Personal Data.
- Written agreements imposing confidentiality and data protection obligations.
- Updates to Subprocessor list as required.
11. Incident response
- Procedures for identifying, investigating, escalating, and responding to security incidents.
- Customer notification procedures for Personal Data Breaches as described in this DPA.
12. Data retention and deletion
- Retention according to the Agreement, Privacy Policy, product configuration, and legal obligations.
- Deletion, anonymization, or return of Customer Data following termination or expiration, subject to backup, legal, security, and compliance exceptions.
Schedule 4 — International Transfers
1. General transfer mechanism
Where Syrix transfers Personal Data internationally, Syrix will rely on lawful transfer mechanisms as required by Applicable Data Protection Laws.
These mechanisms may include:
- Adequacy decisions.
- Standard Contractual Clauses.
- UK Addendum.
- Data processing agreements.
- Subprocessor contractual safeguards.
- Other lawful mechanisms available under Applicable Data Protection Laws.
2. EEA transfers
Where Personal Data subject to the GDPR is transferred to a country that has not been recognized as providing an adequate level of protection, the SCCs will apply as required.
For purposes of the SCCs:
- Customer is the data exporter.
- Syrix is the data importer.
- Module Two, Controller to Processor, will apply where Customer is a Controller and Syrix is a Processor.
- The details of Processing are described in Schedule 1.
- Technical and organizational measures are described in Schedule 3.
- Subprocessors are described in Schedule 2.
3. UK transfers
Where Personal Data subject to the UK GDPR is transferred to a country that has not been recognized as providing an adequate level of protection, the UK Addendum will apply as required.
4. Transfer impact assessments
Taking into account the nature of the Services and information available to Syrix, Syrix will provide reasonable information to Customer to support transfer impact assessments where required by Applicable Data Protection Laws.